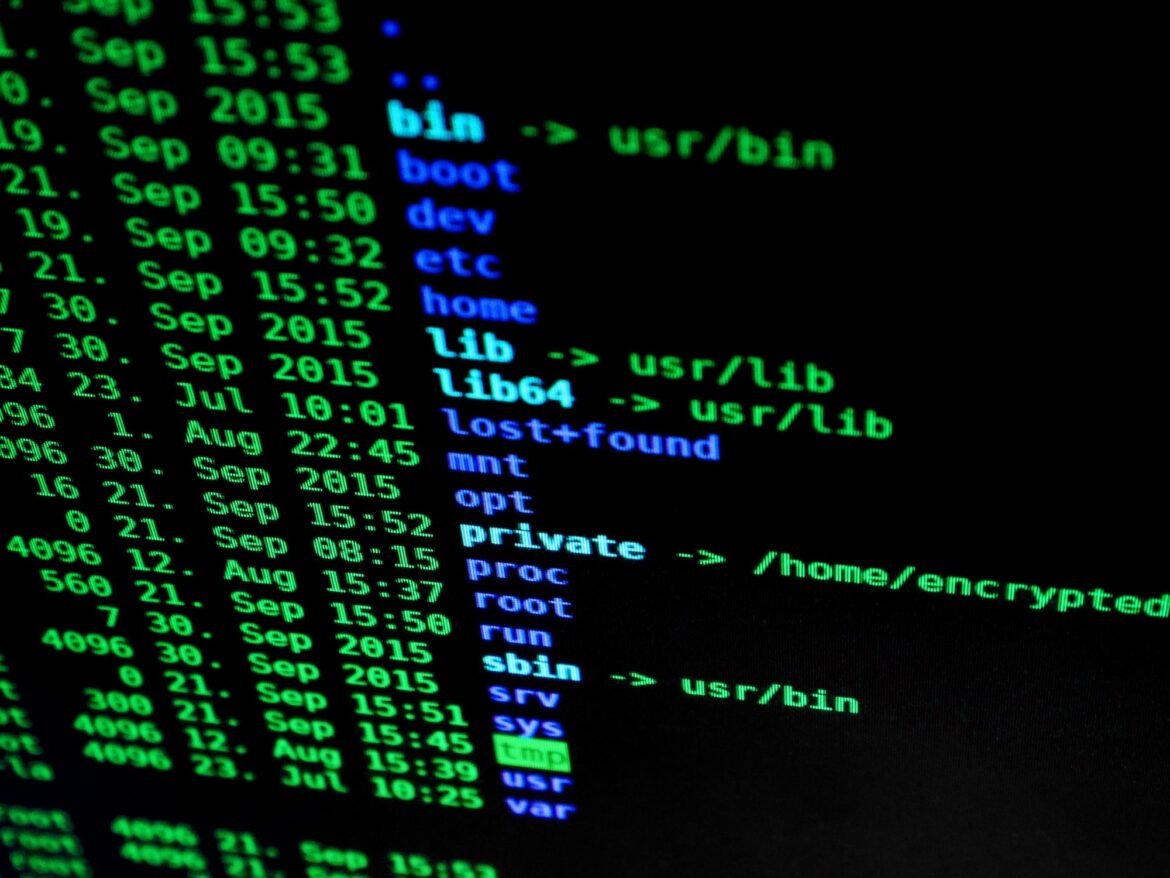
Command Lines
Command lines, also known as command-line interfaces (CLIs), are a type of user interface for computers that allow users to interact with their system by typing in commands. Command lines provide much more flexibility and control over the system than graphical user interfaces (GUIs) do. They can be used to automate tasks or access programs and features not available through GUIs.
A few examples of popular command line tools include the Windows command prompt, bash shell on Linux/UNIX systems, Mac OS X terminal window program, and PowerShell from Microsoft. In addition there are many more specialized CLIs such as those found in cryptocurrencies like Bitcoin Core client software or Ethereum Mist wallet application which have specific functions related to managing cryptocurrency wallets & transactions.
To use a CLI you will need some basic knowledge about how they operate; here is an overview:
1) A CLI consists of two parts – the prompt where you enter your commands and the output area where results show up after entering a command. The prompt typically displays something like “$” but may vary depending on what Operating System it’s being used on -for example Bash Shell Prompts usually display “>_” .
2) After opening a CLI tool all you need to do is start entering commands into it one at time starting with any parameters associated with them if needed -parameters help tell the computer exactly how execute each particular task so make sure they’re correct! For instance when using Bitcoin Core Client Software most common parameter would be “-datadir=
3) Once entered correctly each individual instruction will run until either successful completion or an error message appears telling why it wasn’t able complete its task properly; this process repeats itself until all desired operations were completed successfully without errors showing up at end result screen!
4) Last step involves cleaning up after yourself by closing down any open windows/tabs associated with running cli session since leaving these open could potentially lead security vulnerabilities being exploited maliciously against vulnerable machine hosting them so always remember close everything once done working!.